Following the 3-pillar approach to effective security strategy
Technology innovation – the continued evolution of cloud computing, the rapid increase in Internet of Things (IoT) and the growth of Artificial Intelligence (AI) – is expected to drive a 100x increase in connected devices and a 1,000x increase in data traffic by 2020 (2016 Mobility Report, November 2016, Ericsson). Each new device doesn’t just drive traffic, it also dramatically expands the network attack surface - increasing the opportunity of cybercriminals to leverage sophisticated methods to exploit these opportunities.
 In response to the rapidly evolving cybersecurity threat landscape, regulations around the world are upping the pressure on organizations to protect their sensitive customer and operational data. The maximum fine for a data breach in the upcoming European General Data Protection Regulation (GDPR), for example, could be up to 4% of global revenues; enough to put even large organisations out of business.
In response to the rapidly evolving cybersecurity threat landscape, regulations around the world are upping the pressure on organizations to protect their sensitive customer and operational data. The maximum fine for a data breach in the upcoming European General Data Protection Regulation (GDPR), for example, could be up to 4% of global revenues; enough to put even large organisations out of business.
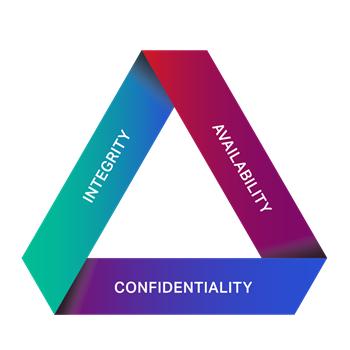
How can an organization minimize its security risks? It’s about more than just encryption and firewalls. A comprehensive, multi-layer security strategy is vital to an effective defense. By following these three key pillars to achieve the confidentiality, integrity, and availability of data in your network, you will be protecting your data, your customers, and your business.
Pillar 1: Confidentiality
The central driving vision for any data security approach is to ensure customer data remains confidential at all times. This requires an end-to-end security solution protecting network traffic from the end point to the data centre.
Data confidentiality in the network begins at the physical layer, where fibre tapping devices can be used to steal sensitive data. To combat this, all your in-flight data should be bulk encrypted from end-to-end, making it undecipherable and, ultimately, useless to hackers.
Another key strategy for enhancing data confidentiality –that also reduces legacy infrastructure costs – is to selectively add service layer encryption at the edge by deploying next-generation, virtualized security solutions in your network. This requires a flexible, open infrastructure that allows you to deliver and provision virtual network functions (VNFs) in real time. Deploying virtual security appliances, including firewalls, intrusion detection systems, and identity/access management systems, while enabling routing of traffic to virtual-honeypots to deceive and detect adversaries, are all part of a multi-layered security solution. In the virtualized security environment, advanced analytics and orchestration tools ensure all VNFs work together effectively.
Pillar 2: Integrity
Data integrity combats cyberattacks by ensuring that information and flows are not altered through unauthorized methods. To achieve true data integrity in the network, you need to trust that the core network elements operate in a trusted state. Network providers and partners should have secure, well-documented life cycle management processes and procedures covering component sourcing and manufacturing, network design, deployment, and operations. Your network partners should also have security accreditations from independent third parties, as well as comply with all the latest security and quality standards. These steps ensure the devices and network elements that pass your critical data have been designed, manufactured, and delivered in a trusted state.
Pillar 3: Availability
Today, data protection legislation requires companies to take technical and organizational measures to ensure the security of data processing. This includes ongoing availability and resilience of processing systems and services, even in the event of a cyberattack or natural disaster. This means your network should incorporate fully redundant infrastructure components including power supplies, processors, and switching fabrics ensuring that traffic is rerouted to an alternative infrastructure if required, and that primary paths are automatically restored as soon as possible.
Availability can be maximized using advanced network analytics. Analytics and reporting identify anomalous network behaviour and empower your operations teams to respond to cyberattacks faster. This approach helps minimize the impact of cyberattacks and gives organizations actionable insights that maximize uptime and improve capacity planning and preventive maintenance.
A well-trained operations team is a key component to maintaining a network. Disaster recovery and incident response training helps the team prepare for cyberattacks quickly and in an appropriate and coordinated manner, minimising the potential impact for your business and your customers. Expect your business partners and vendors to be willing and able to provide training which prepares your operations team for the attacks that are inevitable.
Ensuring the confidentiality, integrity and availability of data in the network
Organizations that make a conscious effort towards implementing a multi-layer security approach have much to gain in the era of high-stake breaches and security risks. As a trusted partner, Ciena’s security capabilities stem from our commitment to secure our business: from protecting our own information assets and those of our partners, to delivering solutions with confidence in the processes and controls that go into the design, deployment and operation of a Ciena-enabled network.
Organizations that make a conscious effort towards implementing a multi-layer security approach have much to gain in the era of high-stake breaches and security risks.
To ensure data remains private and secure, Ciena’s WaveLogic Encryption solutions bulk encrypt all in-flight data end-to-end with no increase in latency, ensuring that data is never compromised by adversaries using “fiber taps”.
As a long-term supplier of carrier-grade networking solutions, Ciena’s established best-practices and controls throughout the entire product development cycle ensure that data traversing a Ciena network is free from unauthorized modifications, so that it arrives to its destination in the exact state that it was sent.
The availability of applications and data is ensured by providing an ultra-high reliable infrastructure, that minimizes downtime, with a full range of protection/restoration mechanisms including fully redundant hardware, a centralized-switched architecture, and multi-layer (L0/L1) control plane for automated, near-real-time restoration.
A comprehensive strategy embeds security consciousness across the fabric of your entire organization; minimizes the attack surface of your network; and prepares your people and infrastructure for future regulatory requirements. Additionally, the right network security partner can help you ensure that all the people, processes and technology that touch your networking operations are completely trustworthy and security oriented. By working with Ciena you can count on the assured infrastructure and network intelligence required to help you mitigate data security risks by ensuring the confidentiality, integrity and availability of data in your network.