What criteria does a layer 1 encryption solution need to meet?
 Tom Engels of Telindus provides a certification checklist to make sure you get the right level of security and compliance with your encryption solution.
Tom Engels of Telindus provides a certification checklist to make sure you get the right level of security and compliance with your encryption solution.
Apollo 10 was a legendary space mission in the Apollo space program. For the first time, live television was broadcast in color from space. This mission was also the dress rehearsal for the moon landing planned for Apollo 11. Nothing was allowed to go wrong during the mission and to ensure this, extensive safety procedures and checklists were used.
When securing your IT infrastructure, you want to make sure that the chosen solution is sufficient. But how do you select a manufacturer and solution that offers the desired level of security and compliancy? National and international certifications can help with making the right decision. Unfortunately, they are often used in the wrong context.
It is important to use a good checklist when selecting a solution, so here is an overview of the relevant certifications you need to know.
1. FIPS certification
The National Institute of Standards and Technology (NIST), is a non-regulatory agency of the U.S. Department of Commerce that publishes standards for encryption algorithms and standards coordinating the requirements and specifications for cryptographic modules. These standards are published as Federal Information Processing Standards (FIPS) publications. FIPS 197 specifies the Advanced Encryption Standard (AES). The requirements regarding cryptographic modules are included in FIPS 140-2. Manufacturers of IT security equipment can have their solution certified by an independent third party against the FIPS standards. NIST issues a certificate and keeps a publicly accessible record of it after positive advice from the test body.
If the requirements change, NIST can withdraw a certificate for a solution or put specific conditions on its use. The FIPS certification for encryption according to FIPS 140-2 is seen worldwide as the benchmark for validating and certifying hardware and software encryption solutions. Both within and outside the government, this certification is at the forefront of the checklist for layer 1 encryption solutions.
Certification on the basis of FIPS 140-2 has four levels, with level 1 being the least stringent in terms of requirements and level 4 the most stringent. This means that a solution that meets the requirements at level 1 offers fewer certainties than those at level 4. At level 1, for example, use can be made of generic chipsets and generic operating systems. Since encryption solutions for WAN connections use specific hardware, a certification at level FIPS 140-2 Level 2 is used as a minimum.
2. Common Criteria
Common Criteria (CC) is an international agreement for the evaluation of security solutions for IT. CC ensures that evaluated and certified solutions are recognized by the other participants in the program. CC has members who can and may issue certificates and members who use certificates.
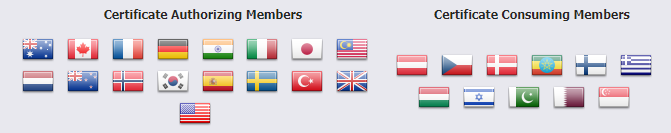
To prevent double certification for the same products, the so-called SOG-IS Mutual Recognition Agreement (MRA) has been drawn up in Europe. The members recognize the certificates (based on Common Criteria or ITSEC) issued by qualified participants. Qualified participants are countries that are allowed to issue SOG-IS certificates.
3. BSI certification
At the European level, BSI certification is sometimes misunderstood. BSI is the German Federal Office for Security in Information Technology. At local level (Germany), BSI-VS-NfD issues certificates (Verschlusssache-Nur für den Dienstgebrauch). A VS-NfD certificate can be recognized by the number BSI-VSA-xxxxx.
In addition to the local VS-NfD certification, the BSI also certifies Common Criteria. Here is where it becomes interesting. Germany is a qualified participant in the SOGIS MRA agreement. This means that certificates based on Common Criteria are recognized by the other members. BSI certificates based on Common Criteria can be recognized by their certification number: BSI-DSZ-CC-xxxxx. Because these certificates comply with Common Criteria, they are often used as a basis for local certification, for example by the NBV against a certain classification level. This saves time and costs in a certification process.
Certifications abound
WAN connections must be secured. Certification guarantees that you get what you paid for when it comes to encryption – a solution that meets the required criteria. The FIPS certification for encryption according to FIPS 140-2 is seen worldwide as the benchmark for encryption hardware and software. In addition to FIPS, there are also the Common Criteria. The ideal combination is a solution that is certified against both FIPS and CC. Just like with a space mission, it is important that your encryption solution is highly secure, so ensure the correct certification. Do you want to know more about the right certifications? Ciena and Telindus are here to help, contact us!
Learn more about Telindus here.
For additional information on the certifications discussed above:
- Common Criteria Portal
- The list of German IT certificates and certified manufacturers and solutions is available online